The Mispadu banking trojan is a type of malware that targets financial institutions in Latin America. This trojan has been active since 2019, and it has affected thousands of users in the region. It is designed to steal sensitive banking information from victims, including login credentials, credit card details, and other financial data.
How Does Mispadu Work?
Mispadu spreads through various channels, including phishing campaigns, malicious software downloads, and software vulnerabilities. In phishing campaigns, attackers use fake emails and websites to trick users into giving up their personal information. They create convincing emails and websites that mimic legitimate financial institutions and lure victims into entering their login credentials or other sensitive data.
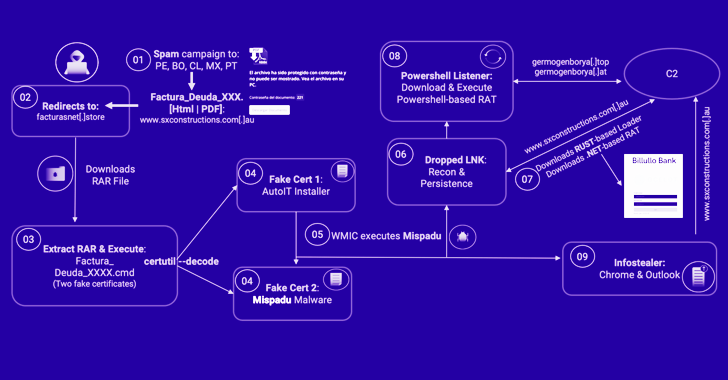
Mispadu also spreads through malicious software downloads. Attackers create fake software downloads that contain the trojan, which can infect users’ computers if they download and run the software. In addition, Mispadu can exploit software vulnerabilities to infect computers without users’ knowledge.
Once Mispadu infects a victim’s computer, it begins to steal sensitive information. The trojan has the ability to capture keystrokes, take screenshots, and record audio and video. It can also modify the DNS settings of the infected computer, redirecting users to fake websites where attackers can collect their personal information.
What Makes Mispadu Dangerous?
Mispadu is a dangerous threat to Latin America because it is designed specifically to target financial institutions in the region. It has been found to target several major banks in Brazil, Mexico, and other countries in the region. Mispadu can steal login credentials, credit card details, and other sensitive information that can be used for fraudulent activities.
The trojan is also difficult to detect and remove. It uses advanced techniques to evade detection by antivirus software, such as encryption and obfuscation. Once installed, it can also disable or modify antivirus software to prevent detection and removal.
Moreover, Mispadu is constantly evolving and updating itself. It has been found to have multiple versions, each with its own unique features and capabilities. This makes it even more difficult to detect and remove from infected computers.
Protecting Against Mispadu
- Users in Latin America can take several steps to protect themselves from the Mispadu banking trojan. First, they should avoid clicking on suspicious links or downloading unknown software. They should only download software from trusted sources and verify the authenticity of emails and websites before entering their personal information.
- Second, users should keep their antivirus software up-to-date. Antivirus software can detect and remove many types of malware, including Mispadu. However, it is important to keep the software up-to-date to ensure that it can detect the latest threats.
- Third, users should regularly back up their important data. This can help protect against data loss in the event of a malware infection. Regular backups can also make it easier to recover from a malware attack.
Conclusion
The Mispadu banking trojan is a dangerous threat to financial institutions and users in Latin America. It is designed to steal sensitive banking information from victims and is difficult to detect and remove. Users in the region should take steps to protect themselves from this threat, including avoiding suspicious links and downloads, keeping their antivirus software up-to-date, and regularly backing up their important data. By taking these steps, users can reduce the risk of falling victim to Mispadu and other types of malware.
